Checkmarx One
This integration allows you to model Checkmarx One resources in your software catalog and ingest data into them.
It lets you map and organize the desired Checkmarx One resources and their metadata in Port (see supported resources below).
Supported Resources
The resources that can be ingested from Checkmarx One into Port are listed below. It is possible to reference any field that appears in the API responses linked below in the mapping configuration.
Project- Project information and metadataScan- Security scan execution details and statusSAST- Static Application Security Testing resultsSCA- Software Composition Analysis resultsKICS- Infrastructure as Code Security resultsContainer Security- Container security scan resultsAPI Security- API security risks and vulnerabilities
Setup
Prerequisites
- A Checkmarx One enterprise account.
- A Port organization with admin permissions.
The Checkmarx One API is available for enterprise customers. You need an API key to authenticate with the Checkmarx One API.
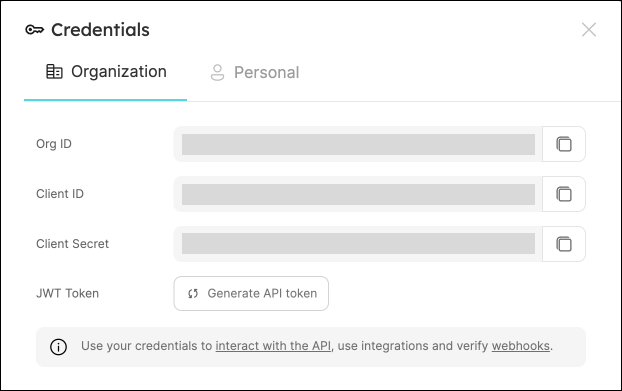
Port Credentials
To get your Port credentials, go to your Port application, click on the ... button in the top right corner, and select Credentials. Here you can view and copy your CLIENT_ID and CLIENT_SECRET:
Checkmarx One Credentials
You need the following connection details to configure Checkmarx One:
- Checkmarx One Base URL: The API endpoint URL for your region
- Checkmarx One IAM URL: The IAM authentication URL for your region
- Tenant Name: Your Checkmarx One tenant name
- API Key: Your Checkmarx One API key
Checkmarx One provides different URLs based on your region:
- US:
https://ast.checkmarx.net/api/https://iam.checkmarx.net - EU:
https://eu.ast.checkmarx.net/api/https://eu.iam.checkmarx.net - US2:
https://us.ast.checkmarx.net/api/https://us.iam.checkmarx.net - EU2:
https://eu-2.ast.checkmarx.net/api/https://eu-2.iam.checkmarx.net - DEU:
https://deu.ast.checkmarx.net/api/https://deu.iam.checkmarx.net - ANZ:
https://anz.ast.checkmarx.net/api/https://anz.iam.checkmarx.net - IND:
https://ind.ast.checkmarx.net/api/https://ind.iam.checkmarx.net - SNG:
https://sng.ast.checkmarx.net/api/https://sng.iam.checkmarx.net - UAE:
https://mea.ast.checkmarx.net/api/https://mea.iam.checkmarx.net
-
Finding Your Checkmarx One Base URL and IAM URL:
- Login to your Checkmarx One account
- Navigate to Settings > Identity and Access Management
- The base URL and IAM URL will be displayed based on your region
- Copy and save both URLs for use in the integration configuration
-
Getting Your Tenant Name:
- Your tenant name is typically part of your login URL
- It can also be found in your account settings
- Copy and save your tenant name
-
Generating an API Key:
- Login to Checkmarx One with admin permissions
- Navigate to Settings > Identity and Access Management > API Keys
- Click Add API Key
- Provide a descriptive name for the API key
- Select the appropriate permissions (read access to projects, scans, and results)
- Click Create API Key
- Copy and securely store the generated API key
Store your API key securely and never share it. The API key provides access to your Checkmarx One data.
Choose one of the following installation methods:
Not sure which method is right for your use case? Check the available installation methods.
- Hosted by Port
- Self-hosted
- CI
Using this installation option means that the integration will be hosted by Port, with a customizable resync interval to ingest data into Port.
Live event support
This integration supports live events, allowing real-time updates to your software catalog without waiting for the next scheduled sync.
Supported live event triggers
- scan_completed_successfully
- scan_failed
- scan_partial
Alternatively, you can install the integration using the Self-hosted method to update Port in real time using webhooks.
Installation
To install, follow these steps:
-
Go to the Data sources page of your portal.
-
Click on the
+ Data sourcebutton in the top-right corner. -
Click on the relevant integration in the list.
-
Under
Select your installation method, chooseHosted by Port. -
Configure the
integration settingsandapplication settingsas you wish (see below for details).
Application settings
Every integration hosted by Port has the following customizable application settings, which are configurable after installation:
-
Resync interval: The frequency at which Port will ingest data from the integration. There are various options available, ranging from every 1 hour to once a day. If a sync is still in progress when the next one is due, the new sync will be skipped (up to 24 hours delay).
This ensures that all kinds are fully synchronized and that cleanup of stale entities always takes place at the end of each sync. -
Send raw data examples: A boolean toggle (enabledby default). If enabled, raw data examples will be sent from the integration to Port. These examples are used when testing your mapping configuration, they allow you to run yourjqexpressions against real data and see the results.
Integration settings
Every integration has its own tool-specific settings, under the Integration settings section.
Each of these settings has an ⓘ icon next to it, which you can hover over to see a description of the setting.
Port secrets
Some integration settings require sensitive pieces of data, such as tokens.
For these settings, Port secrets will be used, ensuring that your sensitive data is encrypted and secure.
When filling in such a setting, its value will be obscured (shown as ••••••••).
For each such setting, Port will automatically create a secret in your organization.
To see all secrets in your organization, follow these steps.
Limitations
- The maximum time for a full sync to run is based on the configured resync interval. For very large amounts of data where a resync operation is expected to take longer, please use a longer interval.
Port source IP addresses
When using this installation method, Port will make outbound calls to your 3rd-party applications from static IP addresses.
You may need to add these addresses to your allowlist, in order to allow Port to interact with the integrated service:
- Europe (EU)
- United States (US)
54.73.167.226
63.33.143.237
54.76.185.219
3.234.37.33
54.225.172.136
3.225.234.99
Using this installation option means that the integration will be able to update Port in real time using polling.
Prerequisites
To install the integration, you need a Kubernetes cluster that the integration's container chart will be deployed to.
Please make sure that you have kubectl and helm installed on your machine, and that your kubectl CLI is connected to the Kubernetes cluster where you plan to install the integration.
If you are having trouble installing this integration, please refer to these troubleshooting steps.
For details about the available parameters for the installation, see the table below.
- Helm
- ArgoCD
To install the integration using Helm:
-
Go to the CheckmarxOne data source page in your portal.
-
Select the
Real-time and always onmethod: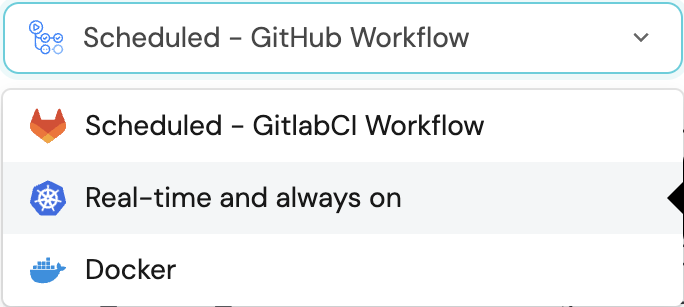
-
A
helmcommand will be displayed, with default values already filled out (e.g. your Port client ID, client secret, etc).
Copy the command, replace the placeholders with your values, then run it in your terminal to install the integration.
BaseUrl & webhook configuration
integration.config.appHost is deprecated: Please use liveEvents.baseUrl for webhook URL settings instead.
In order for the CheckmarxOne integration to update the data in Port on real-time changes in CheckmarxOne, you need to specify the liveEvents.baseUrl parameter.
The liveEvents.baseUrl parameter should be set to the url of your CheckmarxOne integration instance. Your integration instance needs to have the option to setup webhooks via http requests/recieve http requests , so please configure your network accordingly.
To test webhooks or live event delivery to your local environment, expose your local pod or service to the internet using ngrok:
ngrok http http://localhost:8000
This will provide a public URL you can use for webhook configuration and external callbacks during development.
If liveEvents.baseUrl is not provided, the integration will continue to function correctly. In such a configuration, to retrieve the latest information from the target system, the scheduledResyncInterval parameter has to be set, or a manual resync will need to be triggered through Port's UI.
Scalable Mode for Large Integrations
If you are deploying the integration at scale and want to decouple the resync process from the live events process (recommended for large or high-throughput environments), you can enable scalable mode by adding the following flags to your Helm install command:
--set workload.kind="CronJob" \
--set workload.cron.resyncTimeoutMinutes=60 \
--set scheduledResyncInterval="'*/60 * * * *'" \
--set liveEvents.worker.enabled=true
The port_region, port.baseUrl, portBaseUrl, port_base_url and OCEAN__PORT__BASE_URL parameters are used to select which instance of Port API will be used.
Port exposes two API instances, one for the EU region of Port, and one for the US region of Port.
- If you use the EU region of Port (https://app.port.io), your API URL is
https://api.port.io. - If you use the US region of Port (https://app.us.port.io), your API URL is
https://api.us.port.io.
To install the integration using ArgoCD:
- Create a
values.yamlfile inargocd/my-ocean-checkmarx-one-integrationin your git repository with the content:
Remember to replace the placeholders for checkmarxTenant and checkmarxApiKey.
initializePortResources: true
scheduledResyncInterval: 120
integration:
identifier: my-ocean-checkmarx-one-integration
type: checkmarx-one
eventListener:
type: POLLING
config:
checkmarxBaseUrl: https://ast.checkmarx.net/api
checkmarxIamUrl: https://iam.checkmarx.net
checkmarxTenant: CHECKMARX_TENANT_NAME
secrets:
checkmarxApiKey: CHECKMARX_API_KEY
- Install the
my-ocean-checkmarx-one-integrationArgoCD Application by creating the followingmy-ocean-checkmarx-one-integration.yamlmanifest:
Remember to replace the placeholders for YOUR_PORT_CLIENT_ID YOUR_PORT_CLIENT_SECRET and YOUR_GIT_REPO_URL.
Multiple sources ArgoCD documentation can be found here.
::: The Port exposes two API instances, one for the EU region of Port, and one for the US region of Port.ArgoCD Application (click to expand)
apiVersion: argoproj.io/v1alpha1
kind: Application
metadata:
name: my-ocean-checkmarx-one-integration
namespace: argocd
spec:
destination:
server: https://kubernetes.default.svc
namespace: my-ocean-checkmarx-one-integration
project: default
sources:
- repoURL: 'https://port-labs.github.io/helm-charts/'
chart: port-ocean
targetRevision: 0.9.5
helm:
valueFiles:
- $values/argocd/
my-ocean-checkmarx-one-integration/values.yaml
parameters:
- name: port.clientId
value: YOUR_PORT_CLIENT_ID
- name: port.clientSecret
value: YOUR_PORT_CLIENT_SECRET
- name: port.baseUrl
value: https://api.getport.io
- repoURL: YOUR_GIT_REPO_URL
targetRevision: main
ref: values
syncPolicy:
automated:
prune: true
selfHeal: true
syncOptions:
- CreateNamespace=trueport_region, port.baseUrl, portBaseUrl, port_base_url and OCEAN__PORT__BASE_URL parameters are used to select which instance of Port API will be used.
https://api.port.io.https://api.us.port.io.
- Apply your application manifest with
kubectl:
kubectl apply -f my-ocean-checkmarx-one-integration.yaml
This table summarizes the available parameters for the installation. Note the parameters specific to this integration, they are last in the table.
| Parameter | Description | Required |
|---|---|---|
port.clientId | Your port client id (Get the credentials) | ✅ |
port.clientSecret | Your port client secret (Get the credentials) | ✅ |
port.baseUrl | Your Port API URL - https://api.getport.io for EU, https://api.us.getport.io for US | ✅ |
integration.identifier | Change the identifier to describe your integration | ✅ |
integration.type | The integration type | ✅ |
integration.config.appHost | The host of the Port Ocean app. Used to set up the integration endpoint for real-time updates via polling | ✅ |
integration.eventListener.type | The event listener type | ✅ |
scheduledResyncInterval | The number of minutes between each resync | ❌ |
initializePortResources | Default true, When set to true the integration will create default blueprints and the port App config Mapping | ❌ |
sendRawDataExamples | Enable sending raw data examples from the third party API to port for testing and managing the integration mapping. Default is true | ❌ |
integration.config.checkmarxBaseUrl | The Checkmarx One API base URL for your region | ✅ |
integration.config.checkmarxIamUrl | The Checkmarx One IAM URL for your region | ✅ |
integration.config.checkmarxTenant | Your Checkmarx One tenant name | ✅ |
integration.secrets.checkmarxApiKey | Your Checkmarx One API key | ✅ |
integration.secrets.webhookSecret | A secret to secure webhooks from Checkmarx One. This is optional but highly recommended for security if you enable live-events. | ❌ |
For advanced configuration such as proxies or self-signed certificates, click here.
This workflow/pipeline will run the Checkmarx One integration once and then exit, this is useful for scheduled ingestion of data.
If you want the integration to update Port in real time using polling you should use the Self-hosted installation option.
- GitHub
- Jenkins
- Azure Devops
Make sure to configure the following Github Secrets:
| Parameter | Description | Example | Required |
|---|---|---|---|
OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL | The Checkmarx One API base URL for your region | ✅ | |
OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL | The Checkmarx One IAM URL for your region | ✅ | |
OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT | Your Checkmarx One tenant name | ✅ | |
OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY | Your Checkmarx One API key | ✅ | |
OCEAN__INTEGRATION__SECRETS__WEBHOOK_SECRET | A secret to secure webhooks from Checkmarx One. This is optional but highly recommended for security if you enable live-events. | ❌ | |
OCEAN__BASE_URL | The URL of your Checkmarx One integration instance, used for real-time updates | ❌ | |
OCEAN__PORT__CLIENT_ID | Your Port client (How to get the credentials) id | ✅ | |
OCEAN__PORT__CLIENT_SECRET | Your Port client (How to get the credentials) secret | ✅ | |
OCEAN__PORT__BASE_URL | Your Port API URL - https://api.getport.io for EU, https://api.us.getport.io for US | ✅ | |
OCEAN__INITIALIZE_PORT_RESOURCES | Default true, When set to true the integration will create default blueprints and the port App config Mapping. Read more about initializePortResources | ❌ | |
OCEAN__INTEGRATION__IDENTIFIER | The identifier of the integration that will be installed | ❌ |
Here is an example for checkmarx-one-integration.yml workflow file:
name: Checkmarx One Exporter Workflow
on:
workflow_dispatch:
schedule:
- cron: '0 */1 * * *' # Determines the scheduled interval for this workflow. This example runs every hour.
jobs:
run-integration:
runs-on: ubuntu-latest
timeout-minutes: 30 # Set a time limit for the job
steps:
- uses: port-labs/ocean-sail@v1
with:
type: 'checkmarx-one'
port_client_id: ${{ secrets.OCEAN__PORT__CLIENT_ID }}
port_client_secret: ${{ secrets.OCEAN__PORT__CLIENT_SECRET }}
port_base_url: https://api.getport.io
config: |
checkmarx_base_url: ${{ secrets.OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL }}
checkmarx_iam_url: ${{ secrets.OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL }}
checkmarx_tenant: ${{ secrets.OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT }}
checkmarx_api_key: ${{ secrets.OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY }}
Your Jenkins agent should be able to run docker commands.
Make sure to configure the following Jenkins Credentials
of Secret Text type:
| Parameter | Description | Example | Required |
|---|---|---|---|
OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL | The Checkmarx One API base URL for your region | ✅ | |
OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL | The Checkmarx One IAM URL for your region | ✅ | |
OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT | Your Checkmarx One tenant name | ✅ | |
OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY | Your Checkmarx One API key | ✅ | |
OCEAN__INTEGRATION__SECRETS__WEBHOOK_SECRET | A secret to secure webhooks from Checkmarx One. This is optional but highly recommended for security if you enable live-events. | ❌ | |
OCEAN__BASE_URL | The URL of your Checkmarx One integration instance, used for real-time updates | ❌ | |
OCEAN__PORT__CLIENT_ID | Your Port client (How to get the credentials) id | ✅ | |
OCEAN__PORT__CLIENT_SECRET | Your Port client (How to get the credentials) secret | ✅ | |
OCEAN__PORT__BASE_URL | Your Port API URL - https://api.getport.io for EU, https://api.us.getport.io for US | ✅ | |
OCEAN__INITIALIZE_PORT_RESOURCES | Default true, When set to true the integration will create default blueprints and the port App config Mapping. Read more about initializePortResources | ❌ | |
OCEAN__INTEGRATION__IDENTIFIER | The identifier of the integration that will be installed | ❌ |
Here is an example for Jenkinsfile groovy pipeline file:
pipeline {
agent any
stages {
stage('Run Checkmarx One Integration') {
steps {
script {
withCredentials([
string(credentialsId: 'OCEAN__PORT__CLIENT_ID', variable: 'OCEAN__PORT__CLIENT_ID'),
string(credentialsId: 'OCEAN__PORT__CLIENT_SECRET', variable: 'OCEAN__PORT__CLIENT_SECRET'),
string(credentialsId: 'OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL', variable: 'OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL'),
string(credentialsId: 'OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL', variable: 'OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL'),
string(credentialsId: 'OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT', variable: 'OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT'),
string(credentialsId: 'OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY', variable: 'OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY'),
]) {
sh('''
#Set Docker image and run the container
integration_type="checkmarx-one"
version="latest"
image_name="ghcr.io/port-labs/port-ocean-${integration_type}:${version}"
docker run -i --rm --platform=linux/amd64 \
-e OCEAN__EVENT_LISTENER='{"type":"ONCE"}' \
-e OCEAN__INITIALIZE_PORT_RESOURCES=true \
-e OCEAN__SEND_RAW_DATA_EXAMPLES=true \
-e OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL=$OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL \
-e OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL=$OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL \
-e OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT=$OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT \
-e OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY=$OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY \
-e OCEAN__PORT__CLIENT_ID=$OCEAN__PORT__CLIENT_ID \
-e OCEAN__PORT__CLIENT_SECRET=$OCEAN__PORT__CLIENT_SECRET \
-e OCEAN__PORT__BASE_URL='https://api.getport.io' \
$image_name
exit $?
''')
}
}
}
}
}
}
Your Azure DevOps agent should be able to run docker commands.
Make sure to configure the following Azure DevOps Variables as secret variables:
| Parameter | Description | Example | Required |
|---|---|---|---|
OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL | The Checkmarx One API base URL for your region | ✅ | |
OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL | The Checkmarx One IAM URL for your region | ✅ | |
OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT | Your Checkmarx One tenant name | ✅ | |
OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY | Your Checkmarx One API key | ✅ | |
OCEAN__INTEGRATION__SECRETS__WEBHOOK_SECRET | A secret to secure webhooks from Checkmarx One. This is optional but highly recommended for security if you enable live-events. | ❌ | |
OCEAN__BASE_URL | The URL of your Checkmarx One integration instance, used for real-time updates | ❌ | |
OCEAN__PORT__CLIENT_ID | Your Port client (How to get the credentials) id | ✅ | |
OCEAN__PORT__CLIENT_SECRET | Your Port client (How to get the credentials) secret | ✅ | |
OCEAN__PORT__BASE_URL | Your Port API URL - https://api.getport.io for EU, https://api.us.getport.io for US | ✅ | |
OCEAN__INITIALIZE_PORT_RESOURCES | Default true, When set to true the integration will create default blueprints and the port App config Mapping. Read more about initializePortResources | ❌ | |
OCEAN__INTEGRATION__IDENTIFIER | The identifier of the integration that will be installed | ❌ |
Here is an example for checkmarx-one-integration.yml pipeline file:
trigger:
- main
pool:
vmImage: "ubuntu-latest"
variables:
- group: port-ocean-credentials
steps:
- script: |
# Set Docker image and run the container
integration_type="checkmarx-one"
version="latest"
image_name="ghcr.io/port-labs/port-ocean-$integration_type:$version"
docker run -i --rm \
-e OCEAN__EVENT_LISTENER='{"type":"ONCE"}' \
-e OCEAN__INITIALIZE_PORT_RESOURCES=true \
-e OCEAN__SEND_RAW_DATA_EXAMPLES=true \
-e OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL=$(OCEAN__INTEGRATION__CONFIG__CHECKMARX_BASE_URL) \
-e OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL=$(OCEAN__INTEGRATION__CONFIG__CHECKMARX_IAM_URL) \
-e OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT=$(OCEAN__INTEGRATION__CONFIG__CHECKMARX_TENANT) \
-e OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY=$(OCEAN__INTEGRATION__SECRETS__CHECKMARX_API_KEY) \
-e OCEAN__PORT__CLIENT_ID=$(OCEAN__PORT__CLIENT_ID) \
-e OCEAN__PORT__CLIENT_SECRET=$(OCEAN__PORT__CLIENT_SECRET) \
-e OCEAN__PORT__BASE_URL='https://api.getport.io' \
$image_name
exit $?
displayName: 'Ingest Data into Port'
The port_region, port.baseUrl, portBaseUrl, port_base_url and OCEAN__PORT__BASE_URL parameters are used to select which instance of Port API will be used.
Port exposes two API instances, one for the EU region of Port, and one for the US region of Port.
- If you use the EU region of Port (https://app.port.io), your API URL is
https://api.port.io. - If you use the US region of Port (https://app.us.port.io), your API URL is
https://api.us.port.io.
For advanced configuration such as proxies or self-signed certificates, click here.
Configuration
Port integrations use a YAML mapping block to ingest data from the third-party api into Port.
The mapping makes use of the JQ JSON processor to select, modify, concatenate, transform and perform other operations on existing fields and values from the integration API.
Default mapping configuration
This is the default mapping configuration for this integration:
Default mapping configuration (click to expand)
createMissingRelatedEntities: true
deleteDependentEntities: true
resources:
- kind: project
selector:
query: 'true'
port:
entity:
mappings:
blueprint: '"checkmarxProject"'
identifier: .id
title: .name
properties:
name: .name
createdAt: .createdAt
updatedAt: .updatedAt
tags: (.tags // {})
repoUrl: .repoUrl
mainBranch: .mainBranch
origin: .origin
criticality: .criticality
- kind: scan
selector:
query: 'true'
port:
entity:
mappings:
blueprint: '"checkmarxScan"'
identifier: .id
title: '(.projectId + "-" + .id)'
properties:
status: .status
branch: .branch
createdAt: .createdAt
updatedAt: .updatedAt
projectId: .projectId
userAgent: .userAgent
configs: (.configs // {})
statusDetails: (.statusDetails // [])
relations:
project: .projectId
- kind: sast
selector:
query: 'true'
port:
entity:
mappings:
identifier: .resultHash
title: .queryName
blueprint: '"checkmarxSast"'
properties:
firstScanId: .firstScanID
status: .status
state: .state
severity: (.severity // empty)
confidenceLevel: .confidenceLevel
created: .firstFoundAt
nodes: (.nodes // empty)
cweId: (.cweID // empty)
relations:
scan: .scanID
- kind: sca
selector:
query: 'true'
port:
entity:
mappings:
identifier: .id
title: .data.packageIdentifier
blueprint: '"checkmarxSCA"'
properties:
firstScanId: .firstScanId
status: .status
state: .state
severity: .severity
created: .created
description: .description
packageIdentifier: .data.packageIdentifier
recommendations: .data.recommendations
recommendedVersion: .data.recommendedVersion
packageData: .data.packageData
cweId: .vulnerabilityDetails.cweId
relations:
scan: .__scan_id
- kind: kics
selector:
query: 'true'
port:
entity:
mappings:
identifier: .id
title: .description
blueprint: '"checkmarxKics"'
properties:
type: .type
firstScanId: .firstScanId
id: .id
status: .status
state: .state
severity: (.severity // empty)
confidenceLevel: .confidenceLevel
created: .created
description: .description
fileName: (.data.fileName // empty)
line: (.data.line // empty)
platform: (.data.platform // empty)
issueType: (.data.issueType // empty)
expectedValue: (.data.expectedValue // empty)
value: (.data.value // empty)
relations:
scan: .__scan_id
- kind: containers
selector:
query: 'true'
port:
entity:
mappings:
identifier: .id
title: .id
blueprint: '"checkmarxContainerSecurity"'
properties:
firstScanId: .firstScanId
status: .status
state: .state
severity: .severity
confidenceLevel: .confidenceLevel
created: .created
description: .description
packageName: .data.packageName
packageVersion: .data.packageVersion
imageName: .data.imageName
imageTag: .data.imageTag
imageFilePath: .data.imageFilePath
cweId: .vulnerabilityDetails.cweId
relations:
scan: .__scan_id
- kind: apisec
selector:
query: 'true'
port:
entity:
mappings:
identifier: .risk_id
title: .name
blueprint: '"checkmarxApiSec"'
properties:
riskId: .risk_id
apiId: .api_id
severity: (.severity // empty)
name: .name
status: .status
httpMethod: .http_method
url: .url
origin: .origin
documented: .documented
authenticated: .authenticated
discoveryDate: .discovery_date
scanId: .scan_id
sastRiskId: (.sast_risk_id // empty)
projectId: .project_id
state: .state
relations:
scan: .scan_id
If you need to ingest deep links back to the Checkmarx One dashboard, you can construct them using jq expressions in your mapping configuration. Combine your Checkmarx One UI base URL with relevant path parameters from the data returned by the API.
For example, to create a dashboard link for a project:
dashboardUrl: '"https://your-region.ast.checkmarx.net/projects/" + .id'
Or for a specific scan result:
scanUrl: '"https://your-region.ast.checkmarx.net/projects/" + .projectId + "/scans/" + "?id=" + .id'
Replace your-region with your actual Checkmarx One region (e.g., eu, us, deu, etc.) and adjust the path structure based on your Checkmarx One dashboard URL format.
Monitoring and sync status
To learn more about how to monitor and check the sync status of your integration, see the relevant documentation.
Examples
To view and test the integration's mapping against examples of the third-party API responses, use the jq playground in your data sources page. Find the integration in the list of data sources and click on it to open the playground.
Examples of blueprints and the relevant integration configurations can be found on the Checkmarx examples page.
Resource Configuration
The Checkmarx One integration supports filtering and configuration for different resource types:
Project Resources
Projects can be synchronized without additional filtering options.
Scan Resources
Scans can be filtered using the following scan filter options:
- Project Names (
projectIds): Filter scans by their project name - Branches: Filter results by the name of the Git branch that was scanned
- Statuses: Filter results by the execution status of the scans (case insensitive, OR operator for multiple statuses):
QueuedRunningCompletedFailedPartialCanceled
- Since: Filter results by the date and time when the scan was created (UNIX timestamp in seconds, default: 90 days)
Security Scan Results (SCA/Containers) Configuration
You can configure security scan results (SCA, Container Security) with the following filters:
- Scan Filter: Apply the same scan filtering options as above
- Severity: Filter by severity level (
CRITICAL,HIGH,MEDIUM,LOW,INFO) - State: Filter by state:
TO_VERIFYCONFIRMEDURGENTNOT_EXPLOITABLEPROPOSED_NOT_EXPLOITABLEFALSE_POSITIVE
- Status: Filter by status (
NEW,RECURRENT,FIXED) - Exclude Result Types: Filter to exclude dev and test dependencies (
DEV_AND_TEST,NONE)
SAST (Static Application Security Testing) Configuration
SAST results can be configured with comprehensive filtering options:
- Scan Filter: Apply the same scan filtering options as above
- Compliance: Filter by compliance standard (exact match, case insensitive)
- Group: Filter by vulnerability group (substring match)
- Include Nodes: Include or omit node data (default:
true) - Language: Filter by language (exact match, case insensitive)
- Result ID: Filter by unique result hash
- Severity: Filter by severity level (
critical,high,medium,low,info) - Status: Filter by status (
new,recurrent,fixed) - Category: Filter by comma separated list of categories
- State: Filter by state:
to_verifynot_exploitableproposed_not_exploitableconfirmedurgent
KICS (Infrastructure as Code Security) Configuration
KICS results can be configured with the following filters:
- Scan Filter: Apply the same scan filtering options as above
- Severity: Filter KICS results by severity levels (
CRITICAL,HIGH,MEDIUM,LOW,INFO) - Status: Filter KICS results by status (
NEW,RECURRENT,FIXED)
API Security Configuration
API security results can be configured with:
- Scan Filter: Apply the same scan filtering options as above
Troubleshooting
Common Issues
- Authentication Errors: Ensure your API key is valid and has the correct permissions
- Regional URL Issues: Verify you're using the correct base URL and IAM URL for your region
- Tenant Name Issues: Make sure your tenant name is correctly specified
- Permission Issues: Ensure your API key has read access to projects, scans, and results
Logs and Debugging
The integration provides detailed logging for debugging:
- Check the integration logs for authentication and API request details
- Verify that the correct URLs and credentials are being used
- Monitor for any rate limiting or permission errors
For more detailed troubleshooting, refer to the Checkmarx One API documentation.
Alternative installation via webhook
While the Ocean integration described above is the recommended installation method, you may prefer to use a webhook to ingest data from Checkmarx One. If so, use the following instructions:
Note that when using the webhook installation method, data will be ingested into Port only when the webhook is triggered.
Webhook installation (click to expand)
In this example you are going to create a webhook integration between Checkmarx One and Port, which will ingest Checkmarx One scan events and results.
Port configuration
Create the following blueprint definitions:Checkmarx Scan blueprint (click to expand)
{
"identifier": "checkmarxScan",
"title": "Checkmarx Scan",
"icon": "Checkmarx",
"schema": {
"properties": {
"status": {
"type": "string",
"title": "Status",
"enum": [
"Queued",
"Running",
"Completed",
"Failed",
"Partial",
"Canceled"
],
"description": "The status of the scan. Possible values: Queued, Running, Completed, Failed, Partial, Canceled."
},
"branch": {
"type": "string",
"title": "Branch",
"description": "The branch of the repository that was scanned."
},
"createdAt": {
"type": "string",
"format": "date-time",
"title": "Created At",
"description": "The date and time when the scan was created."
},
"updatedAt": {
"type": "string",
"format": "date-time",
"title": "Updated At",
"description": "The date and time when the scan was last updated."
},
"projectId": {
"type": "string",
"title": "Project ID",
"description": "The identifier of the project to which this scan belongs."
},
"userAgent": {
"type": "string",
"title": "User Agent",
"description": "The user agent used to initiate the scan."
}
},
"required": ["status", "projectId"]
},
"relations": {}
}
Create the following webhook configuration using Port's UICheckmarx One webhook configuration (click to expand)
Checkmarx One mapper;checkmarx_one_mapper;A webhook configuration to map Checkmarx One scan events to Port;Checkmarx;{
"mappings": [
{
"blueprint": "checkmarxScan",
"itemsToParse": ".body",
"entity": {
"identifier": ".item.scanId",
"title": "(.item.projectId + \"-\" + .item.scanId)",
"properties": {
"status": ".item.status",
"branch": ".item.branch",
"createdAt": ".item.createdAt",
"updatedAt": ".item.updatedAt",
"projectId": ".item.projectId",
"userAgent": ".item.userAgent"
}
}
}
],
"enabled": true,
"security": {}
}
Create a webhook in Checkmarx One
You can follow the instruction in Checkmarx One's webhook documentation, they are also outlined here for reference:
- Log in to Checkmarx One with admin permissions.
- Navigate to Settings > Webhooks.
- Click Add Webhook.
- Input the following details:
Name- use a meaningful name such as Port Webhook.Payload URL- enter the value of theurlkey you received after creating the webhook configuration.- Under
Events- select the following events:Project CreatedCompleted ScanFailed ScanPartial Scan
- Click Create Webhook at the bottom of the page.
In order to view the different payloads and events available in Checkmarx One webhooks, look here
Done! any project creation and scan completion event (successful, failed, or partial) will trigger a webhook event that Checkmarx One will send to the webhook URL provided by Port. Port will parse the events according to the mapping and update the catalog entities accordingly.
Webhook Configuration Options
Checkmarx One supports two types of webhook configurations with different scoping levels:
Tenant-Level Webhooks
- Scope: Receive events from all projects within your Checkmarx One tenant
- Use Case: When you want to monitor all security scans across your entire organization
- Configuration: Set up the webhook at the tenant level in Checkmarx One settings
- Events: All scan events (
scan_completed_successfully,scan_failed,scan_partial) from any project
Project-Scoped Webhooks
- Scope: Receive events only from specific projects you select
- Use Case: When you want to monitor only certain critical projects or applications
- Configuration: Set up the webhook at the project level in Checkmarx One settings
- Events: Scan events only from the selected project(s)
- Use tenant-level webhooks for comprehensive security monitoring across your organization
- Use project-scoped webhooks when you need granular control or want to reduce noise from non-critical projects
Let's Test It
This section includes a sample webhook event sent from Checkmarx One when a scan is completed. In addition, it includes the entity created from the event based on the webhook configuration provided in the previous section.
Payload
Here is an example of the payload structure sent to the webhook URL when a Checkmarx One scan is completed:Webhook event payload (click to expand)
{
"id": "f62213cb-183b-4a48-b880-56640d45d209",
"status": "Running",
"branch": "main",
"createdAt": "2025-09-08T17:39:31.344557Z",
"updatedAt": "2025-09-08T17:39:31.448929Z",
"projectId": "6ace8769-7ad3-4812-8990-0d4111ba0156",
"projectName": "Test-Project/test-repo",
"userAgent": "grpc-java-netty/1.63.0",
"initiator": "user@company.org",
"tags": {},
"metadata": {
"id": "f62213cb-183b-4a48-b880-56640d45d209",
"type": "git",
"Handler": {
"GitHandler": {
"branch": "main",
"repo_url": "https://github.com/Test-Org/test-repo",
"credentials": {
"type": "apiKey",
"value": "*****",
"username": "*****"
}
}
},
"configs": [
{
"type": "sast",
"value": {
"presetName": "",
"incremental": "false"
}
},
{
"type": "sca"
},
{
"type": "kics"
},
{
"type": "apisec"
}
],
"project": {
"id": "6ace8769-7ad3-4812-8990-0d4111ba0156"
},
"created_at": {
"nanos": 128635019,
"seconds": 1757353171
}
},
"engines": [
"sast",
"sca",
"kics",
"apisec"
],
"sourceType": "github",
"sourceOrigin": "Project Scan"
}
Mapping Result
The combination of the sample payload and the webhook configuration generates the following Port entity:
{
"identifier": "f62213cb-183b-4a48-b880-56640d45d209",
"title": "6ace8769-7ad3-4812-8990-0d4111ba0156-f62213cb-183b-4a48-b880-56640d45d209",
"blueprint": "checkmarxScan",
"properties": {
"status": "Running",
"branch": "main",
"createdAt": "2025-09-08T17:39:31.344557Z",
"updatedAt": "2025-09-08T17:39:31.448929Z",
"projectId": "6ace8769-7ad3-4812-8990-0d4111ba0156",
"userAgent": "grpc-java-netty/1.63.0",
"configs": {},
"statusDetails": []
},
"relations": {
"project": "6ace8769-7ad3-4812-8990-0d4111ba0156"
}
}